Clone a git repository with submodules using init and update example
Clone Git submodules example
If you have a Git repository with submodules, you’ll likely be surprised to find out that when you clone the repository, it does not bring down all of the branches and code for the associate submodules.
A few extra steps need to be taken.
Git clone with submodules
The list of steps required to clone a Git repository with submodules is:
- Issue a git clone command on the parent repository.
- Issue a git submodule init command.
- Issue a git submodule update command.
The git submodule init and update commands are needed to pull down submodule artifacts and resources.
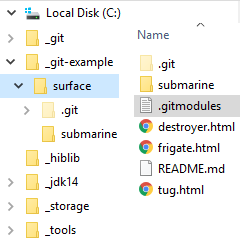
When these three steps are complete, both the parent repository and all submodules will be available locally.
Files from the master branch of the parent repository and the submodule will be available in their respective git working trees.
Git init and update alternative
There is actually an alternative to going through these three steps. You can use the –recurse-submodules switch on the clone. This approach, shown below, might be easier.
git clone --recurse-submodules https://github.com/cameronmcnz/surface.git Git submodule clone
The commands issued to clone the git repository and all submodules are:
submodule@example:~$ git clone https://github.com/cameronmcnz/surface.git submodule@example:~$ git submodule init submodule@example:~$ git submodule update
The clone operation will obviously happen after multiple repositories have been created and submodules added to them. For more information on how to perform other git submodule operations, check out our full listing of “git submodule how to” tutorials.
You can find both of these repositories on GitHub and GitLab.



